Context:
- 2023 saw a surge in cyber events globally.
- Forescout’s 2023 Threat Roundup reports attacks from 212 countries, highlighting a significant rise from China.
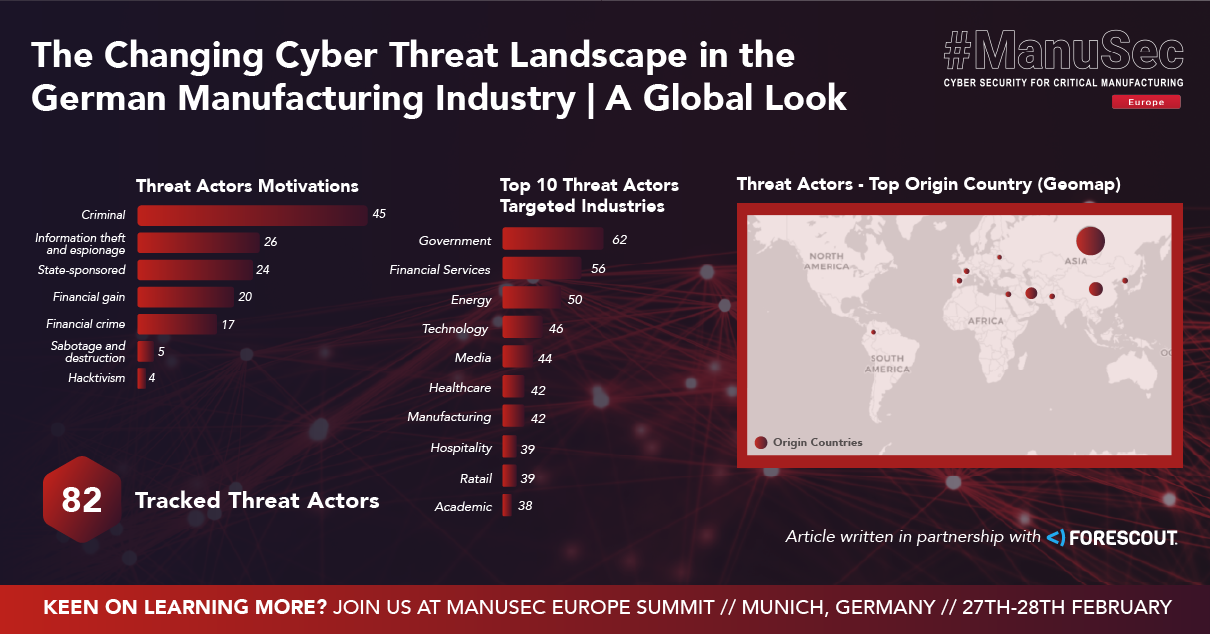
- Around 600 threat actors targeted 163 countries, with the U.S., U.K., Germany, India, and Japan facing the brunt. China, Russia, and Iran were major sources of these threats.
- Compromised devices, especially those managed by ISPs, were commonly used in attacks.
Key Findings:
- Web applications and remote management services were primary targets.
- There was a notable increase in attacks against network infrastructure and IoT devices.
- Operational Technology (OT) faced consistent threats, with specific OT protocols being targeted.
- Post-exploitation actions mainly included persistence, discovery, and execution.
- RATs and information stealers were the most prevalent malware.
- Cobalt Strike remained the top command and control architecture.
A Closer Look at Germany:
- Germany faced significant cyber threats, with 82 of the 600 tracked actors focusing on the region.
- Government and manufacturing were primary targets, indicating a complex threat landscape involving nation-state and non-state actors.
Final Remarks
- The manufacturing sector’s growing digital integration increases its vulnerability to sophisticated attacks.
- Manufacturers must prioritize cybersecurity through comprehensive strategies including risk assessments, employee training, and advanced security measures.
Keen on learning more? Join Forescout at ManuSec Europe Summit in Munich on 27th-28th of February, 2024.
Article written in partnership with Forescout.